Ensure you keep your device, personal information, and data safe as houses
Apple has a strong track record regarding security and privacy. Often, it’s individual users – people – that are the weak link. But there are things you can do to safeguard the digital life that you lead with your iPhone – and elsewhere.
Our tips may in some cases require some setting up and a little extra ongoing overhead. But implement them in your daily life and you’ll be significantly more protected against nefarious individuals and companies.
Secure your Apple ID with two-factor authentication
Two-factor authentication has been described as ‘something you know’ combined with ‘something you have’. Often, it’s a combination of password and physical device, making it much harder for someone to break into your account.
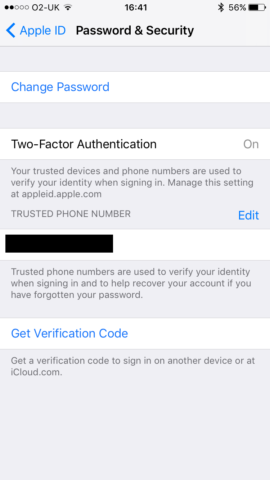
On your iPhone, tap your name in Settings and then Password & Security. Tap Turn on Two-Factor Authentication. Enter your trusted phone number. If someone tries to sign into your account, your iPhone will get an alert. Note that other services also offer two-factor authentication, including those by Google and Dropbox. Investigate and activate them too.
Rethink passwords and security questions
People are often lazy when it comes to passwords. Never use something very simple, and be aware it’s also not clever to memorise a single password that’s only slightly amended for each login. After all, if someone (or some software) can figure out the pattern, all of your passwords are at risk.
For best results, you should use a password manager, with semi-randomised strings of characters. If you want a memorable password for a specific often-used service, four words separated by hyphens or spaces should do. But never reuse them across multiple services.
Also, security questions can be socially engineered. (If an account is ‘protected’ by your mother’s maiden name, for example, that’s no protection at all.) Therefore, make the answers to these questions like any other password, and note them down somewhere secure for later use.
Activate iCloud Keychain
Under your name in Settings, go to iCloud > Keychain and turn on iCloud Keychain. Enter your Apple ID password and follow the instructions. Once this is set up, your passwords, payment information, and Wi-Fi network sign-ins will be synced across your approved devices.
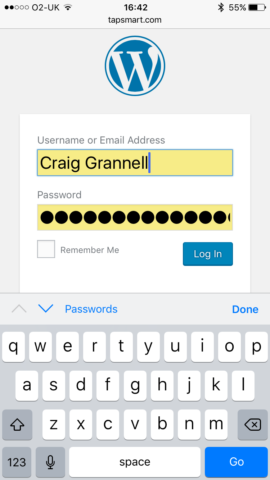
This also means that when Safari suggests a password for a new site, you can accept what it offers, rather than trying to fashion something memorable (and, likely, less secure) yourself.
For subsequent inputs, Safari will optionally auto-populate sign-in and payment fields, excepting three-figure security codes for cards during purchases. (They must always be entered manually.)
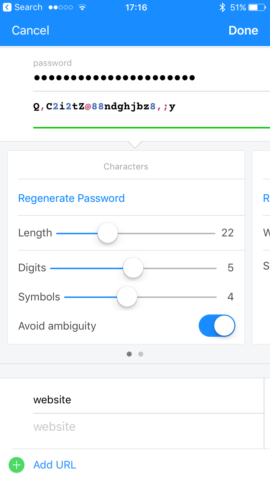
Check out 1Password
A free download for iPhone, 1Password is a password manager and secure wallet that has some overlap with iCloud Keychain. In which case, you might wonder why we’re recommending it.
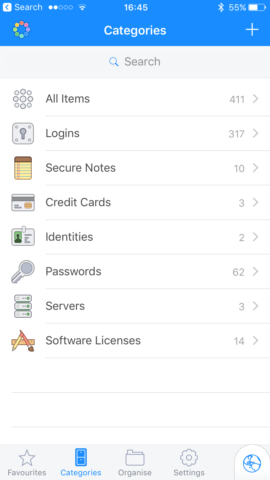
First, 1Password is fully cross-platform, and although it’s not quite as integrated with Safari as Apple’s solution, it’s a decent alternative if you use Windows and Android.
Otherwise, it’s useful for being a repository for other kinds of data you’d like to keep secure (web servers; notes; software licenses), and you can also use it to create custom logins/passwords for websites and security questions.
Use Touch ID and other iPhone security
In Settings, use Touch ID & Passcode to set up a six-digit passcode for your iPhone. If your device has Touch ID, use that to unlock it, since your fingerprint is tough to forge.
Within this area of Settings, you can also restrict access to specific kinds of data when your iPhone is locked, including Today View, Notifications View, and the ability to reply with a message. (This is recommended if you have personal information appear in those places, such as calendar events.)
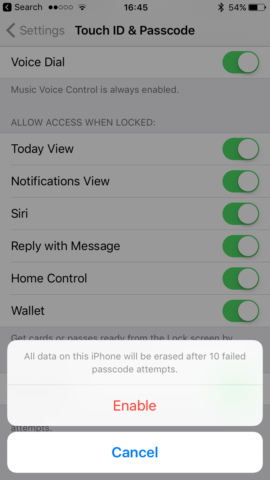
The final option, Erase Data, will erase data from the iPhone if someone gets the passcode wrong ten times. This is worth turning on, in case your iPhone is ever stolen. However, do be mindful if a curious toddler gets hold of your phone, they might unsuccessfully try to unlock it the requisite number of times!
Set up Find my iPhone
Under your name in Settings, choose iCloud and then Find My iPhone. Turn the feature on, along with Send Last Location. Through the Find My iPhone app (and its equivalent on the likes of iCloud.com), you can find the most recently broadcast location of a device.
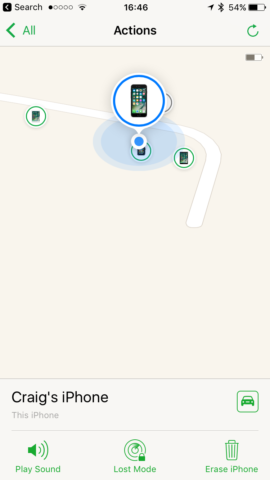
Select a device and then Actions and you can have it blare a sound if it’s ‘lost’ nearby. If your iPhone’s somewhere you don’t expect it to be, you can place it in Lost Mode (which remotely locks the device and displays a message aimed at whoever’s found it), or as a last resort remote-wipe it using the Erase option.
Be wary of app permissions
Generally speaking, apps are well-behaved on iOS, only asking for permission when they really need it. However, if an app asks for permissions you don’t want it to have, deny them. (If you later change your mind, not least if an app fails to work, you can adjust permissions settings using the big app list in Settings.)
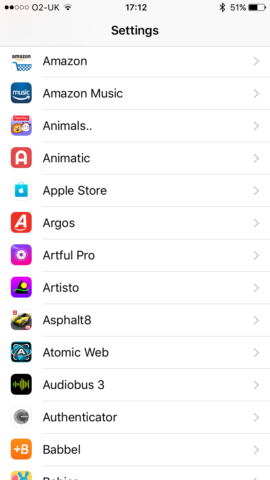
This tip also extends to permissions within apps. If you use a Facebook sign-in, check what details the app’s asking for. Your public profile? Fair enough. Your entire friends list? That may well be a step too far.
Restrict online sharing
Be very aware of what you openly share online. Search engines gulp down everything they find, which in theory becomes searchable and accessible forever.
With social media, consider making feeds with personal information only accessible to friends (and not friends of friends) and manage your lists to only include people you trust. If you’ve something very personal to share, do so via a very restricted list.
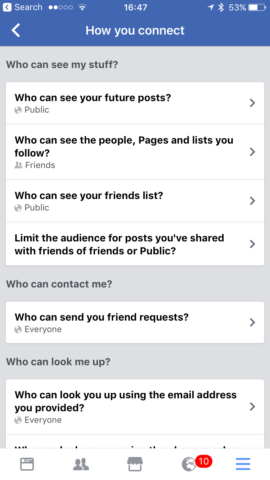
Also, recognise what you post online isn’t always just about you. If you’re always posting about your children, for example, obfuscate their names and dial back on publicly posted imagery – after all, they may otherwise get a shock the first time they search for themselves online and discover a slew of links and photos. (To share pictures, you can use iCloud Photo Sharing or set up a restricted group in Facebook.)
Be vigilant of scams and cons
When you receive an email claiming one of your accounts has been hijacked in some manner, it could be a phishing scam. In fact, it more often than not is.
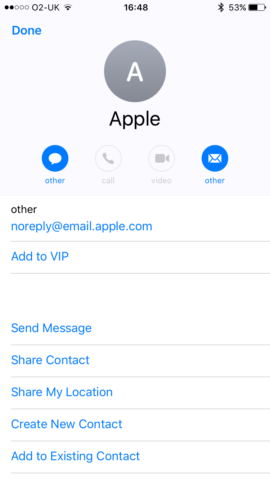
Under such circumstances, do not click the sign-in link. Investigate the address the email was sent from, to see if it’s suspicious. (The depicted one is a genuine email from Apple.) If you’re concerned about an account, sign in elsewhere, check things are OK, and possibly change your password.
Keep devices updated
Finally, updating iOS can be a pain, but make sure you do so anyway. The latest version of your iPhone’s operating system often contains security fixes alongside bug fixes. Without them, your iPhone’s less secure, regardless of whatever else you do.