In the wake of Apple’s public battle with the FBI over encryption and privacy, a team of German hackers has demonstrated a severe weakness in the worldwide mobile network system. This flaw allows calls to be tapped, text messages to be intercepted and even physical location to be inferred.
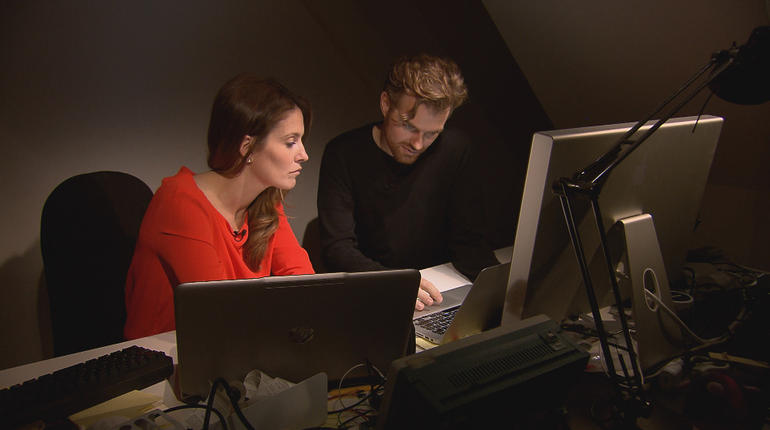
Congressman Ted Lieu, willing participant in the test, was given a brand new iPhone by the team at CBS News’ 60 Minutes, who then provided the hackers with nothing but Lieu’s phone number. The vulnerabilities were demoed during a hacking conference in Berlin, during which the team replayed recordings from Lieu’s iPhone. They also showed how “cellphone tower triangulation” could be used to calculate a user’s whereabouts, even with GPS features disabled.
The good news for Apple customers is that this flaw isn’t directly linked to the iPhone – it’s an issue with the networks used for all mobile communications. Meaning that this isn’t due to an iOS bug or some other oversight by Apple. The bad news, of course, is that pretty much every phone around the world is vulnerable to being surveilled in this way. Apparently this knowledge is an “open secret among the world’s intelligence agencies,” who aren’t exactly keen for it to be fixed as it provides them an easy way to tap phone calls.
One way to avoid leaving your communications open to this vulnerability is to use systems that aren’t linked to a telecom network. For example, iMessages and FaceTime calls (both audio and video) are encrypted end-to-end and sent over the internet rather than through a cell network, thereby avoiding this vulnerability completely. This is one way in which iPhone users can benefit from increased security, and the recent decision by Whatsapp to use end-to-end encryption is a good messaging solution for those without an iOS device (or who want to chat to those without an iOS device).